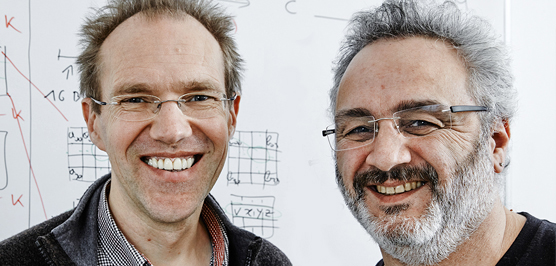
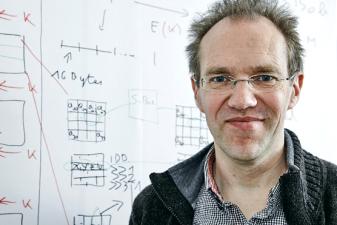
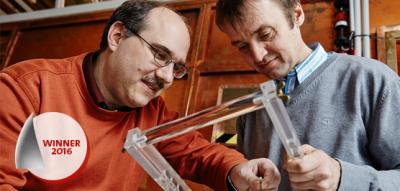
Joan Daemen, Pierre-Yvan Liardet
Secure smart-card encryption
Finalist for the European Inventor Award 2016
Smart cards - credit, banking and other security cards equipped with a tell-tale, gold-coloured, square contact pad - have increasingly replaced "traditional" magnetic-strip-based technology. They have been commonplace in many European countries since the mid-1990s and have since been incorporated into banking and credit cards in the US. The small gold pad includes memory banks, and sometimes microprocessors, that not only store important information for quick access, they also help protect against a full range of security threats.
But while the first generations of smart cards had intrinsic "smart" security, it was not truly brilliant. Would-be criminals could exploit a loophole in how smart cards were produced, creating duplicate copies of cards by gaining access to a master card. This master card is used to individualise large numbers of "recipient" cards that are distributed to card holders.
A team of Belgian and French inventors, led by Daemen and Liardet, found a way to close this security vulnerability by encrypting master cards with a security algorithm that ensures they can never be used to clone or gain access to recipient cards at a later time.
Societal benefit
Until these new security features were invented, all it took to compromise more than one smart card - or an entire network, for that matter - was to gain access to the master card. If a company issuing smart cards became aware of a breach, it had no choice but to cancel and replace every card in the network. That could be a costly and inconvenient endeavour, especially considering that there were about 9 billion smart cards issued in 2015. Most of those (5.1 billion) went to the telecom sector, while another 2.6 billion were used in debit or credit cards.
A security breach not only represented high costs for the company issuing the cards, it could also have economic and privacy ramifications for card users. Recipients' bank accounts, identity and personal information would be potentially vulnerable, wreaking havoc on unsuspecting consumers and clients.
Economic benefit
A booming market for mobile electronic devices will likely bolster smart-card sales for the foreseeable future, most notably in encrypted SIM cards used to manage mobile data and communications accounts. Manufacturers of payment cards such as Europay, MasterCard and Visa (EMV) are also issuing more cards with embedded circuits than with the traditional magnetic strip.
These trends have led some market researchers to estimate that the global smart-card market will enjoy compound annual growth of around 9% over the next several years, driving the industry's overall valuation up to EUR 10.4 billion by 2020.
Daemen, Liardet and their team's invention has a direct impact on this industry, since better encryption algorithms facilitate wider adoption of smart cards. According to the European Central Bank, for every EUR 2 635 that is spent via credit card, EUR 1 is lost to fraud.
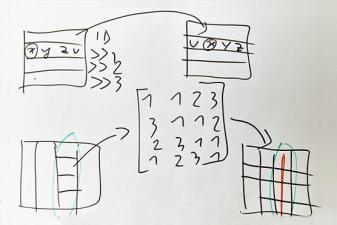
How it works
The invention's advantage is that it allows a master card to communicate with a recipient card only one time. During that first (and last) interaction, the master card sends an encryption key to a recipient card and in turn, the card sends a confirmation back that the key has been received.
Then, and only then, can the master card proceed with recording data onto the recipient card. In addition, without that confirmation, the master card cannot continue recording other cards. In fact, it cannot issue any new cards unless the exact prior recipient card is present. This means that even if a master card were to fall into the wrong hands, it's effectively useless. Not only is communication with recipient cards a one-time event, but a compromised master card is also unable to issue any new cards.
The inventors
Joan Daemen was born in Neerpelt, Belgium, and went on to study civil engineering at KU Leuven, where he was awarded a PhD in cryptography. Daemen quickly rose to become one of the world's leading minds in encryption algorithms and data security. He worked for a number of companies, including Proton World, where he was employed when the United States government put out the call for a new industry standard for encrypting electronic data.
His block cipher, which he developed with his colleague Vincent Rijmen, was eventually adopted by the National Institute of Standards and Technology as its Advanced Encryption Standard. Soon thereafter, Proton World was acquired in 2003 by STMicroelectronics for what was then around EUR 60 million (AUD 110 Million). In 2014, STMicroelectronics generated annual revenues of EUR 6.7 billion.
French cryptographer Liardet has spent nearly a quarter of a century improving smart-card security and developing enhanced security codes and protocols. Since 1998 he has worked at STMicroelectronics, after holding positions at both Schlumberger and Solaic Smartcard, where he likewise supported the deployment of EMV cryptographic security. Liardet is the co-author of seven internal publications and co-inventor on more than 50 patents (45 approved or pending European patent families). He received his PhD in computer science from the Montpellier Laboratory of Informatics, Robotics and Microelectronics (LIRMM) in 2006, having written his dissertation on ways to defend against sneaky side-channel attacks (SCA).
Did you know?
One of the earliest known ciphers is the Caesar cipher, named after Julius Caesar, who used it to protect messages exchanged with his army. Encrypting messages according to this cipher requires substituting each letter for another letter a certain number of places down the alphabet. If, for example, the original message were, "Get a better cipher", and there was a right shift of three, the new message would read, "Jhw d ehwwhu flskhu".
Ciphers have advanced much since then: the Advanced Encryption Standard is based on an algorithm that performs even more complex shifting or substitution than the Caesar cipher, using at least ten rounds of processing along with other permutations and distinct keys to make deciphering an encoded message extremely time-consuming. Using today's fastest supercomputers, it is estimated that it would take something of the order of a billion billion years (3.4 x 1038) to crack AES's most basic (128-bit) encryption key by sending randomly generated combinations in a "brute force attack".
Media gallery
Contact
European Inventor Award and Young Inventors Prize queries:
european-inventor@epo.org Subscribe to the European Inventor Award newsletterMedia-related queries:
Contact our Press team#InventorAward #YoungInventors